What is Cybersecurity and Why Is It Important in 2025? – A Complete Guide for Beginners
Introduction: Why Cybersecurity Matters More Than Ever
We live in a time where everything from banking, shopping, learning, and working happens online. While technology has made life easier, it has also made us more vulnerable to digital threats.
Think about this:
- You use your smartphone to make payments
- You store important documents on cloud drives
- Your home has smart gadgets like cameras, speakers, or even fridges
All of these devices are connected to the internet. But with more connectivity comes more risk of hacking, data leaks, and cyberattacks. This is where cybersecurity becomes critical.
Let’s break down what cybersecurity means, why it’s important, and the different types you should know about in 2025—even if you’re just getting started.
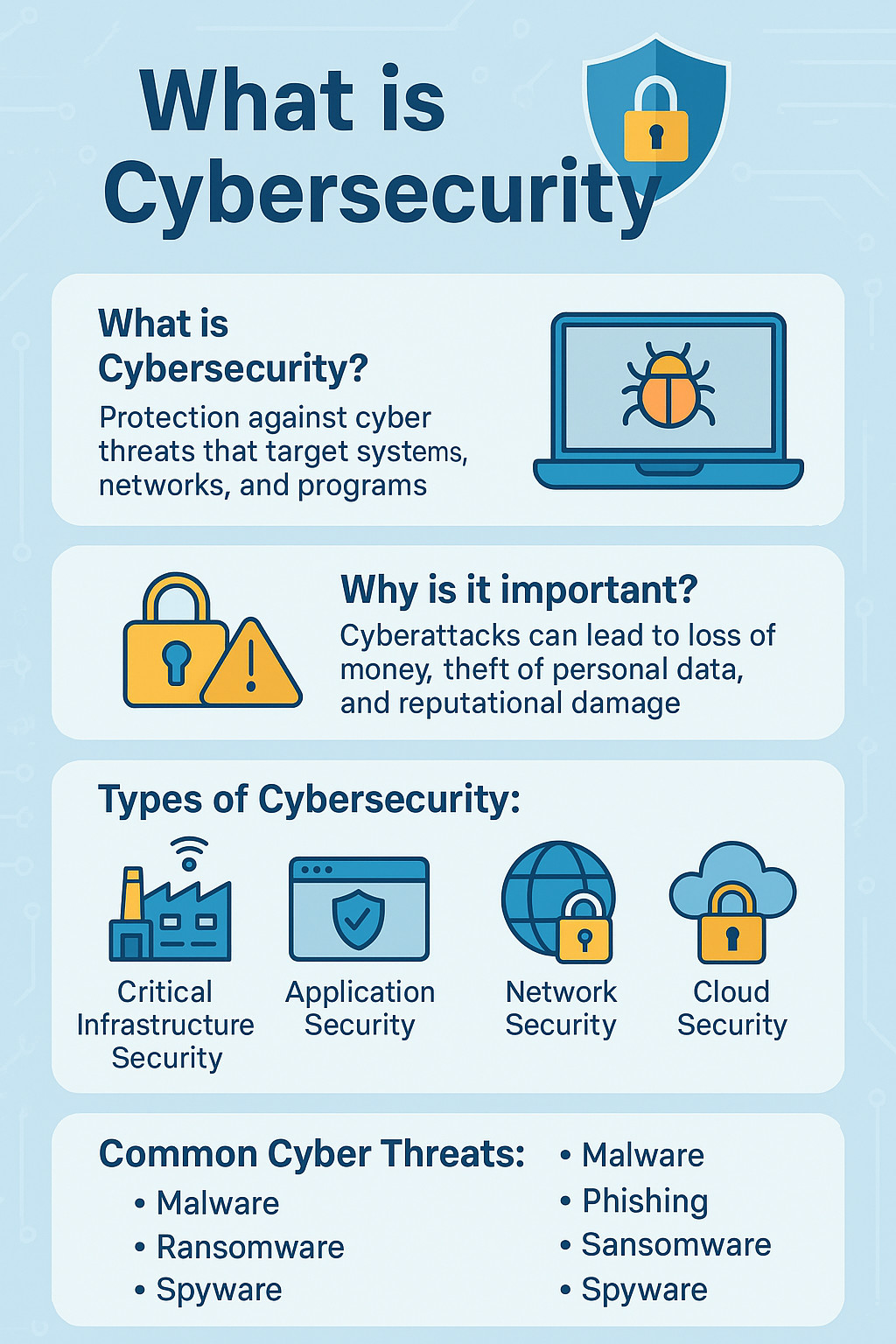
What is Cybersecurity?
Cybersecurity is the process of protecting computers, networks, servers, mobile devices, and data from unauthorized access, attacks, or damage.
It’s like having a lock on your door—but for your digital life.
Cybersecurity protects:
- Your personal details (like passwords, addresses, IDs)
- Your money (bank accounts, payment apps)
- Business information (emails, client data, documents)
- Government systems (e.g., defense, transport, elections)
With strong cybersecurity, your data is safe from hackers, scammers, and malware.
Why is Cybersecurity Important in 2025?
As of 2025, over 6 billion people use the internet. We rely on it for everything. But at the same time, cybercriminals have newer tools like AI and deepfakes to trick or attack us.
Here’s why cybersecurity is more important than ever:
- Hackers can steal your data and sell it on the dark web
- Scammers can pretend to be someone you know using fake profiles
- Companies can lose millions due to cyberattacks and leaks
- Personal gadgets like webcams can be hacked if not protected
- Even kids are targeted online through games, fake links, and messaging apps
Real Example: In a recent case, attackers used a fake email that looked like it came from a bank. Clicking the link led to a fake login page that stole the user’s password.
Cybersecurity helps stop these threats.
What Are the 5 Main Types of Cybersecurity?
Understanding cybersecurity is easier when you know its major areas. Here are 5 core types, simplified for beginners:
1. Critical Infrastructure Security
This type protects essential systems like:
- Power stations
- Hospitals
- Airports
- Government services
These are things we rely on every day. If someone hacks into these, the entire city or country can be affected. Think of it like protecting the backbone of a nation.
Example:
A hacker disables a city’s traffic lights remotely, causing accidents and traffic chaos. Critical infrastructure security prevents this.
2. Application Security
This protects the apps you use on your phone, tablet, or computer—like:
- Online banking apps
- E-commerce platforms
- Food delivery apps
- Email or chat apps
Why it matters: Hackers often try to enter through weak or outdated apps.
Protection methods:
- App updates
- Strong password rules
- Two-factor authentication
- Bug fixes from developers
3. Network Security
Your network connects all your devices to the internet. Network security protects that connection.
This includes:
- Home Wi-Fi
- Office LAN
- Public hotspots
Common threats:
- Viruses
- Spyware
- Phishing
- Data theft over Wi-Fi
Beginner tip:
Always use password-protected Wi-Fi and install firewall software to protect your internet connection.
4. Cloud Security
We now store files, photos, and videos in the cloud—think Google Drive, iCloud, or Dropbox.
Cloud security protects your data stored online.
Features include:
- File encryption
- Multi-device sign-in alerts
- Remote data wipe
- Permission settings (who can access your files)
Note:
Just because data is in the cloud doesn’t mean it’s automatically safe. Always enable two-factor authentication and use strong passwords.
5. IoT (Internet of Things) Security
IoT refers to smart devices connected to the internet. These include:
- Smart TVs
- Fitness bands
- Smart home cameras
- Voice assistants (like Alexa, Google Home)
Unfortunately, many of these devices have weak security.
Risks:
- Hackers spying through smart cameras
- Smart speakers recording private conversations
- Hackers using your smart fridge to attack other networks (yes, that happens!)
How to stay safe:
- Regularly update your devices
- Change default passwords
- Turn off devices when not in use
Common Cybersecurity Threats to Watch for
Even beginners can learn to recognize and avoid common cyber threats. Here are some basic types:
| Threat Type | What It Means |
|---|---|
| Phishing | Fake emails or messages asking for passwords or money |
| Malware | Harmful software like viruses or trojans |
| Ransomware | Hackers lock your files and ask for money to unlock them |
| Spyware | Software that secretly records what you type or see |
| Man-in-the-middle | Someone secretly watching your online activity (like on public Wi-Fi) |
Tips to Stay Safe Online in 2025 (for Everyone!)
Whether you’re a student, employee, or business owner, follow these simple tips:
- Use strong passwords (with numbers, symbols, and no names or birthdays)
- Turn on 2FA (two-factor authentication) for all accounts
- Don’t click links from unknown senders
- Keep your apps and operating system updated
- Install a trusted antivirus program
- Avoid using public Wi-Fi without a VPN
- Don’t reuse the same password across multiple sites
Conclusion: Cybersecurity is Everyone’s Responsibility
Cybersecurity isn’t just for tech experts or big companies anymore—it’s for everyone. Whether you’re browsing the internet, using smart devices, managing a business, or just posting on social media, your online safety is in your hands.
As cyber threats grow in 2025, learning the basics of cybersecurity will protect not just your data—but your peace of mind.
See Also:
Share Your Thoughts
What concerns you most about cybersecurity in 2025? Have you ever faced a cyberattack? Let us know in the comments.
Learn More with IoTDunia
Subscribe to our YouTube Channel for beginner-friendly videos on IoT, AI, and cybersecurity.








Leave a Review