What is CoAP Protocol? A 2025 Guide to the Constrained Application Protocol in IoT
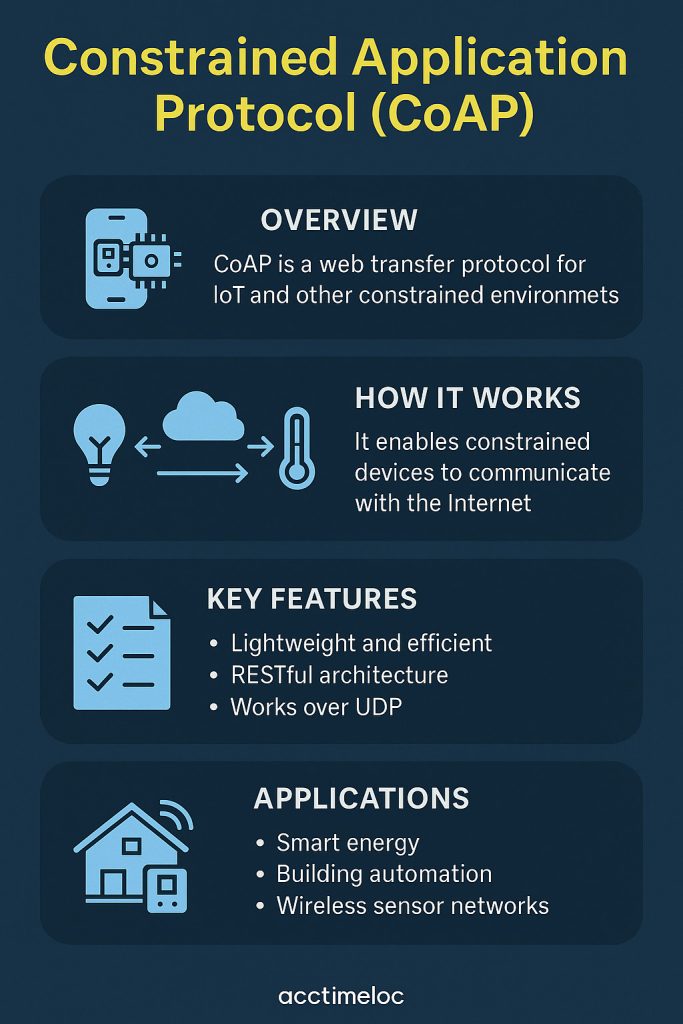
The Constrained Application Protocol (CoAP) is a lightweight web transfer protocol specially built for constrained devices and networks in the Internet of Things (IoT) ecosystem. Designed by the IETF, CoAP operates efficiently on low-power microcontrollers and lossy networks, making it ideal for smart homes, industrial automation, smart agriculture, and energy systems.
As of 2025, CoAP has matured into one of the most reliable and secure communication protocols for Machine-to-Machine (M2M) communication and resource-constrained environments.
What is the CoAP Protocol?
CoAP is a RESTful application-layer protocol inspired by HTTP, but optimized for low-power devices. It works over UDP (User Datagram Protocol), ensuring fast communication with minimal overhead, low bandwidth usage, and support for multicast—all key requirements for IoT and embedded systems.
Key Highlights:
- Built for devices with limited RAM/CPU, like wireless sensors and embedded controllers.
- Uses UDP, instead of TCP, to reduce overhead.
- Supports asynchronous communication and multicast.
- Offers DTLS (Datagram Transport Layer Security) for strong encryption.
- Enables proxying with HTTP—web clients can interact with CoAP resources via CoAP-to-HTTP gateways.
Features & Functions of CoAP
| Feature | Description |
|---|---|
| RESTful API | Uses GET, PUT, POST, DELETE methods like HTTP |
| Compact Messages | Small binary headers (4 bytes minimum) |
| Multicast Support | Efficient for sending the same command to multiple devices |
| Observability | Clients can “observe” resources and get updates when data changes |
| Low Memory Use | Can run on devices with just 10 KiB RAM |
| DTLS Security | Provides robust security comparable to 3072-bit RSA |
| Efficient Caching | Supports freshness indicators for caching responses |
| Proxy Support | Seamlessly connects with web apps via CoAP-HTTP proxies |
How CoAP Works (Architecture Overview)
CoAP uses a simple request/response model similar to HTTP. Here’s how it functions:
- Client sends a request (e.g., GET a temperature reading).
- Server replies with the sensor data.
- Requests and responses use a binary message format with options encoded in a Type-Length-Value (TLV) format.
- Optional tokens are used to match requests with responses.
- Reliability is achieved through retransmissions and acknowledgments.
CoAP messages are designed to fit inside a single UDP packet, making them ideal for low-bandwidth networks like LoRaWAN and NB-IoT.
CoAP Security in 2025
In 2025, IoT security is a major priority. CoAP supports:
- DTLS 1.3 for encrypted communication.
- Device authentication via pre-shared keys, raw public keys, or certificates.
- Replay protection and data integrity.
- Authorization frameworks compatible with OAuth 2.0 for access control.
Even on minimal hardware, CoAP provides enterprise-grade security without compromising performance.
Real-World Applications of CoAP
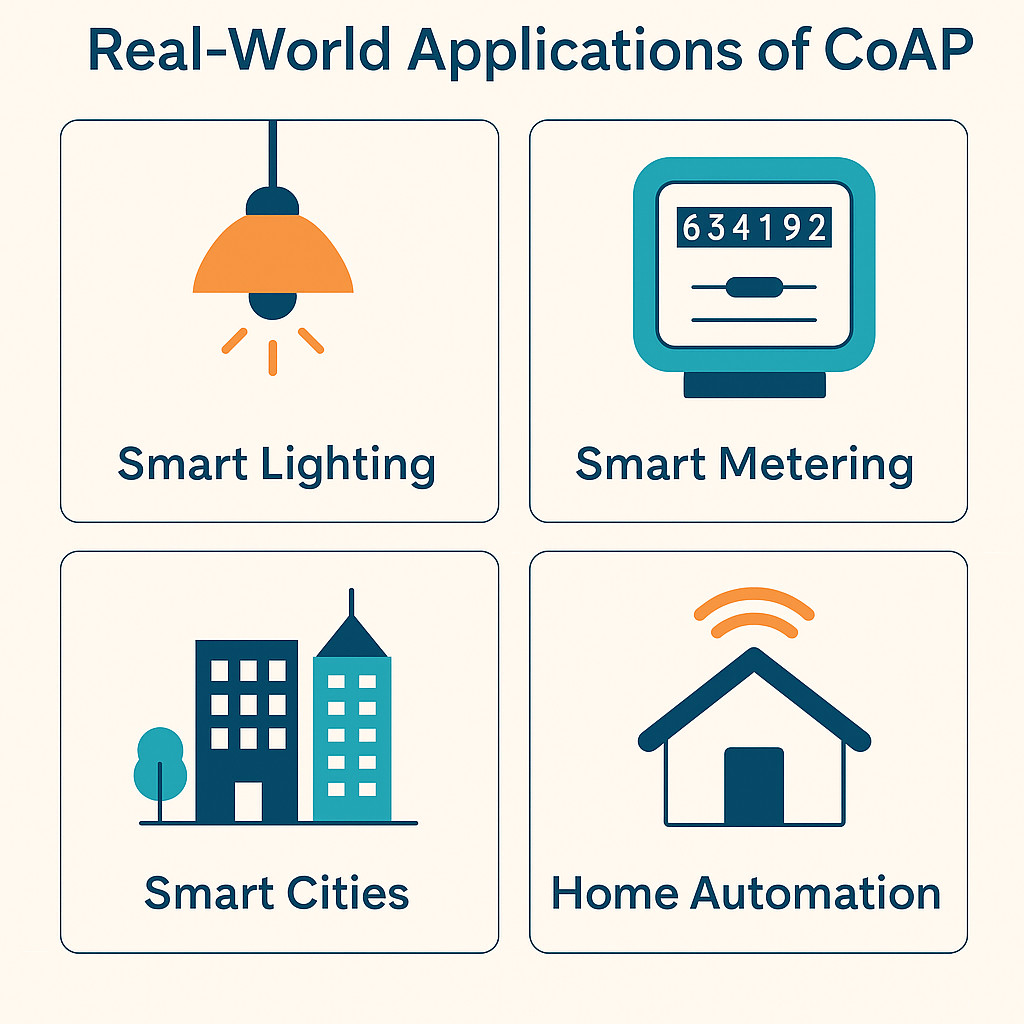
CoAP powers many real-world IoT solutions in 2025:
| Use Case | Description |
|---|---|
| Smart Lighting | Control all lights in a room with one multicast CoAP request |
| Smart Metering | Send periodic meter data from constrained nodes to cloud servers |
| Smart Cities | Enable streetlight sensors and environmental monitors to talk over CoAP |
| Home Automation | Manage temperature sensors, locks, and alarms on local CoAP networks |
| Agritech | Enable low-power farm sensors to communicate with central gateways |
Group Communication in CoAP
CoAP supports group communication via RFC 7390:
- Send a single multicast message to control multiple devices.
- Useful in scenarios like “turn on all lights in this building.”
- However, multicast has reliability trade-offs. An alternative is unicast group forwarding via intermediaries that handle response aggregation.
CoAP vs HTTP vs MQTT (2025 Update)
| Feature | CoAP | HTTP | MQTT |
|---|---|---|---|
| Transport | UDP | TCP | TCP |
| Overhead | Low | High | Low |
| Security | DTLS | TLS | TLS |
| Messaging Model | Request/Response + Observe | Request/Response | Publish/Subscribe |
| Use Case Fit | Sensor nodes, actuators | Web, browsers | Cloud-connected devices |
| Multicast Support | Yes | No | No |
See also: Difference between MQTT and CoAP; CoAP vs MQTT and MQTT and HTTP : Difference between MQTT vs HTPP
Developer Insight: CoAP and REST Integration
Because CoAP mirrors HTTP‘s RESTful nature, IoT developers can:
- Use familiar GET/POST methods.
- Seamlessly translate CoAP requests to HTTP and vice versa.
- Enable web apps to interact with CoAP devices using cross-protocol proxies.
- Leverage existing REST frameworks for faster IoT application development.
CoAP and DoS Amplification Risks
Despite its benefits, CoAP may be misused in DDoS attacks via amplification:
- A small CoAP request may generate a large response.
- Attackers can spoof source IPs and use CoAP nodes to overwhelm a target.
- Proper rate-limiting and secure configurations are essential in production deployments.
Conclusion: Is CoAP the Right Protocol for IoT in 2025?
Yes—CoAP remains one of the most efficient and secure protocols for low-power IoT networks in 2025. It combines the simplicity of HTTP with the performance needed for embedded systems.
Whether you’re working on a smart home system, industrial monitoring, or low-power sensor network, CoAP offers a future-proof, standardized approach to communication.
Frequently Asked Questions (FAQ)
1. What is the CoAP Protocol used for?
Answer:
The Constrained Application Protocol (CoAP) is designed for enabling communication between constrained devices in IoT environments. It is commonly used in applications like smart homes, industrial automation, smart agriculture, and other machine-to-machine (M2M) communications that require low overhead and high efficiency.
2. How is CoAP different from HTTP?
Answer:
CoAP is a lightweight protocol that works over UDP, making it faster and more suitable for constrained networks compared to HTTP, which uses TCP. CoAP also supports multicast, small packet sizes, and lower memory use, making it ideal for embedded devices.
3. Is CoAP a secure protocol?
Answer:
Yes, CoAP uses DTLS (Datagram Transport Layer Security) to ensure data encryption, message integrity, and authentication. It provides robust security even on devices with limited processing capabilities.
4. Can CoAP communicate with HTTP-based systems?
Answer:
Absolutely. CoAP and HTTP both follow RESTful architecture, allowing them to interoperate through CoAP-HTTP proxies. This means IoT devices using CoAP can still be accessed via standard web applications.
5. What transport protocol does CoAP use?
Answer:
CoAP primarily uses UDP to ensure low latency and minimal overhead. It can optionally use DTLS over UDP for added security.
6. Where is CoAP used in real-world applications?
Answer:
CoAP is widely used in smart lighting systems, energy metering, smart agriculture sensors, industrial monitoring, and city infrastructure like environmental monitoring and traffic control.
7. Can CoAP handle group communication?
Answer:
Yes, CoAP supports group communication via multicast (RFC 7390) and unicast forwarding through intermediaries. This allows commands to be sent to multiple devices at once, like turning off all lights in a room with one request.
8. What is the minimum message size in CoAP?
Answer:
The smallest CoAP message is just 4 bytes when excluding optional fields like Token, Options, and Payload. This ultra-compact size helps reduce bandwidth usage and power consumption.
Ready to Explore More? Let’s Build Smarter Together!
Subscribe to Our YouTube Channel » for IoT video Tutorials.
Start Learning IoT Basics Now » and What is IoT? – Introduction to IoT for Beginners on IoTDunia.com!
and Check out Top IoT Applications in Real World – Smart Use Cases 2025, IoT career guide 2025, Best Projects on IoT for Beginners
Have questions? Drop them in the comments!








Leave a Review